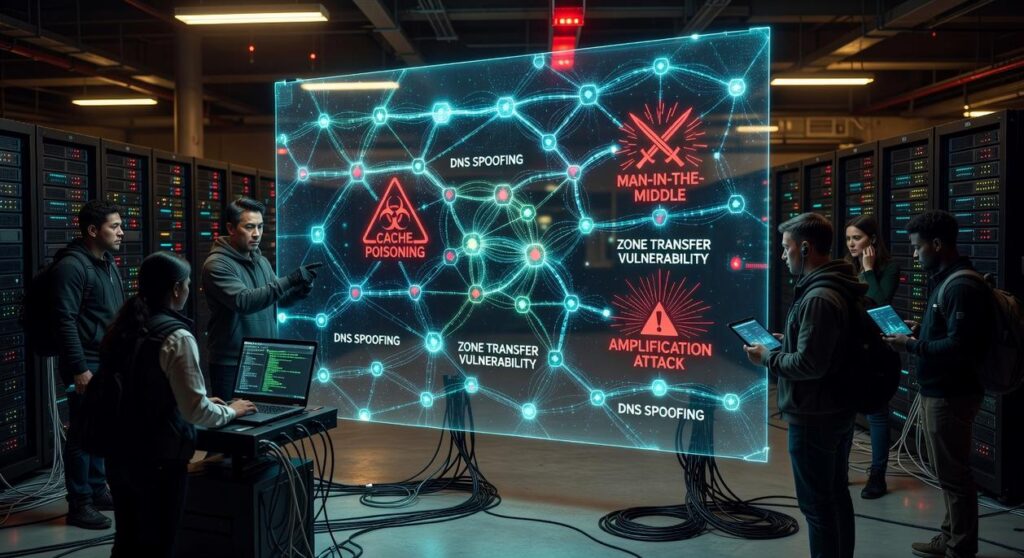
If you’re researching dns exploit risks, you’re likely trying to understand how vulnerabilities in the Domain Name System can expose networks, applications, and devices to serious threats. From cache poisoning and amplification attacks to protocol misconfigurations, DNS remains one of the most overlooked yet frequently targeted layers of internet infrastructure.
This article breaks down how these exploits work, why they persist, and what they mean for modern systems powered by AI tools, connected devices, and cloud-based platforms. You’ll learn where weaknesses typically emerge, how attackers take advantage of them, and what practical steps reduce exposure without overcomplicating your architecture.
Our analysis draws on current security research, real-world vulnerability reports, and hands-on evaluation of protocol behavior across evolving tech environments. The goal is simple: give you a clear, technically grounded understanding of DNS attack surfaces and the defensive strategies that actually make a difference today.
Every click begins with a DNS lookup, yet this foundational system remains dangerously exposed. Over the past 24 months, security firms like Palo Alto Networks and Cloudflare have reported double-digit increases in DNS-based attacks, with DNS tunneling and cache poisoning leading the surge. In 2023, CISA warned that misconfigured resolvers were exploited in ransomware campaigns.
So what does that mean in practice? Attackers intercept queries, inject malicious IP addresses, or exfiltrate data through seemingly harmless requests. These dns exploit risks are not theoretical; the 2024 Akamai report documented billions of daily malicious DNS queries across enterprise networks.
However, awareness alone is insufficient. By mapping protocol-level weaknesses—such as lack of DNSSEC validation and open recursion—you can identify exposure points and implement targeted mitigations before adversaries do.
How DNS Works and Why It’s Inherently Vulnerable
As enterprises increasingly rely on complex digital infrastructures, understanding vulnerabilities like DNS exploits becomes as crucial as staying ahead of technological advancements, such as those discussed in our article on ‘The Future Of 3d Printing Etrstech,’ which highlights the transformative potential of emerging technologies.
Think of DNS as the internet’s phonebook. You type a domain name, and DNS translates it into an IP address computers understand. Without it, browsing would feel like memorizing everyone’s phone number in the Avengers.
That translation process happens constantly and almost instantly.
Here’s the catch: DNS was built for speed, not suspicion. Back in the early internet days, engineers trusted everyone on the network. Security features like authentication were afterthoughts. That trust model means servers accept answers without deeply verifying them, opening the door to dns exploit risks.
Key terms help. A resolver is the middleman that asks for the address. An authoritative server is the source of truth for a domain. A query is the question sent out, and a cache is the temporary memory that stores previous answers.
From an attacker’s perspective, DNS is a single point of failure. Compromise it, and you can redirect traffic, intercept data, or knock services offline. It’s less “hacker magic” and more exploiting a system that assumes everyone plays nice.
Pro tip: enabling DNSSEC adds cryptographic verification, which helps confirm responses are genuine. Still, no system is perfect. Even phonebooks can be forged.
Common DNS Vulnerabilities Explained

The Domain Name System (DNS) is often described as the internet’s phonebook. However, unlike your contacts app, it was not built with modern threat models in mind. As a result, several attack vectors continue to expose organizations to serious dns exploit risks.
DNS Cache Poisoning (Spoofing)
DNS cache poisoning occurs when an attacker injects false DNS records into a resolver’s cache, causing users to be redirected to malicious sites. Instead of reaching your bank, you land on a convincing fake (and yes, it can look pixel-perfect).
A classic example is the 2008 Kaminsky attack, which exploited predictable transaction IDs to flood resolvers with forged responses. Once cached, the malicious entry persisted until expiration. While patches improved randomness and added source port validation, the deeper lesson is architectural: trust without authentication is fragile. DNSSEC was introduced to cryptographically sign responses, yet adoption remains uneven.
DNS Amplification/Reflection (DDoS Attacks)
Next, consider DNS amplification. Attackers send small spoofed queries to open resolvers, forging the victim’s IP address. The resolver then sends a much larger response to the victim, multiplying traffic volume—sometimes by 50x or more (US-CERT).
Step by step, it’s simple: spoof → query → amplify → overwhelm. Some argue basic firewall rules solve this. In reality, misconfigured open resolvers persist globally, making reflection attacks stubbornly effective.
DNS Tunneling
DNS tunneling hides malicious data inside legitimate-looking DNS queries. Attackers encode data into subdomains, enabling exfiltration or command-and-control channels. Because DNS traffic is rarely blocked outright, it often bypasses perimeter defenses. Detection requires behavioral analytics, not just signature scanning.
Domain Hijacking
Finally, domain hijacking differs by layer. Registrar-level hijacking transfers ownership entirely. DNS record manipulation, by contrast, alters A or MX records without changing ownership. Both can reroute traffic or intercept email.
Security gaps often overlap with issues discussed in the hidden risks of outdated ssl and tls versions. Ultimately, DNS resilience demands layered controls, continuous monitoring, and proactive auditing—not blind trust in legacy defaults.
From Theory to Reality: Notable DNS Exploits in Action
The risks of DNS abuse aren’t theoretical—they’ve already reshaped the internet. Consider the Dyn DDoS attack in October 2016. A Mirai-based botnet of roughly 100,000 compromised IoT devices flooded Dyn’s DNS infrastructure with traffic, disrupting Twitter, Netflix, Reddit, and GitHub (U.S. DHS, 2016). Because DNS translates domain names into IP addresses, overwhelming it effectively made major platforms unreachable. The incident exposed systemic fragility: when a core provider fails, downstream services collapse like dominoes.
Similarly, the Sea Turtle campaign (2017–2019) demonstrated state-sponsored DNS hijacking in action. Attackers compromised domain registrars and redirected government and telecom traffic to malicious servers, intercepting credentials and sensitive data (Cisco Talos, 2019). Rather than breaching endpoints directly, they manipulated trust at the resolution layer—subtle, persistent, and difficult to detect.
Meanwhile, modern malware has weaponized DNS itself. The Sunburst backdoor, tied to the SolarWinds breach, used DNS queries for command-and-control (C2), blending malicious traffic with normal lookups (FireEye, 2020). As a result, defenders now treat DNS logs as critical telemetry.
So what does this prove? Simply put, dns exploit risks are operational realities, not edge cases. And as attackers grow more sophisticated, DNS becomes both battleground and early-warning system.
Implementing Layered DNS Hardening
First, enable DNSSEC (Domain Name System Security Extensions), which adds cryptographic signatures to DNS records so resolvers can verify origin and integrity. While some argue DNSSEC is complex and brittle, automated key rotation and modern tooling reduce operational friction. Next, deploy DNS firewalls with Response Policy Zones (RPZ) to block queries to known malicious domains at the resolver level, shrinking dns exploit risks before connections form. Meanwhile, optimize devices by enforcing secure resolvers over DoH or DoT and continuously monitor outbound DNS traffic for anomalies. Pro tip: baseline normal query volume to spot subtle data exfiltration.
Securing your DNS is no longer optional; it’s a competitive advantage. This guide outlined major threats, from cache poisoning to tunneling, but the real benefit is clarity. When you tackle the silent nature of DNS with proactive controls, you dramatically reduce dns exploit risks and gain operational stability.
A multi-layered strategy delivers measurable wins:
- Stronger data integrity through DNSSEC validation
- Fewer malware callbacks with intelligent filtering
- Faster incident response via monitoring
The payoff? Less downtime, improved user trust, and audit-ready visibility. Pro tip: start with a configuration audit today and prioritize security upgrades immediately strategically.
Stay Ahead of Emerging Tech Threats
You came here to better understand how evolving AI tools, machine learning trends, and protocol vulnerabilities impact your systems—and now you have a clearer picture of where the real risks and opportunities lie. From smarter automation to hidden weaknesses in network layers, the landscape is moving fast, and falling behind isn’t an option.
The biggest pain point isn’t just complexity—it’s uncertainty. Unpatched protocol gaps, overlooked device inefficiencies, and rising dns exploit risks can quietly undermine performance and security before you even realize there’s a problem. Staying informed is no longer a luxury; it’s a defensive strategy.
The good news? With the right insights and proactive optimization, you can strengthen your infrastructure, reduce exposure, and confidently leverage AI-driven innovation instead of reacting to threats after damage is done.
If you’re ready to eliminate blind spots, mitigate dns exploit risks, and future-proof your systems with trusted, expert-backed tech intelligence, start applying these strategies today. Don’t wait for a vulnerability to cost you time or data—take control now and stay ahead of the next wave of disruption.

 There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Laurie Moorestevenor has both. They has spent years working with ai tools and machine learning trends in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Laurie tends to approach complex subjects — AI Tools and Machine Learning Trends, Core Tech Concepts and Innovations, Device Optimization Hacks being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Laurie knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Laurie's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in ai tools and machine learning trends, that is probably the best possible outcome, and it's the standard Laurie holds they's own work to.
There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Laurie Moorestevenor has both. They has spent years working with ai tools and machine learning trends in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Laurie tends to approach complex subjects — AI Tools and Machine Learning Trends, Core Tech Concepts and Innovations, Device Optimization Hacks being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Laurie knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Laurie's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in ai tools and machine learning trends, that is probably the best possible outcome, and it's the standard Laurie holds they's own work to.
