Cyber threats are evolving faster than most users and organizations can keep up with—and few are as dangerous or misunderstood as man-in-the-middle exploits. If you’re searching for clear, actionable guidance on man in the middle attack prevention, you likely want more than textbook definitions. You want to understand how these attacks work in real-world environments, how they exploit protocol vulnerabilities, and what practical steps actually reduce your risk.
This article breaks down the mechanics behind interception attacks, highlights common weaknesses in modern networks and devices, and explains how encryption standards, secure configurations, and AI-driven monitoring tools can strengthen your defenses. We draw on current cybersecurity research, emerging machine learning detection models, and documented breach case studies to ensure the insights are accurate and up to date.
By the end, you’ll have a clear, technically grounded roadmap to identify vulnerabilities and implement effective prevention strategies with confidence.
Decoding the Invisible Threat: How Your Data is Intercepted Mid-Transit
Every time you log into a bank account or send a private message, your data travels across networks you do not control. Without safeguards, attackers can quietly intercept and even alter that information—a classic man in the middle attack.
To reduce this risk, start with HTTPS everywhere and enforce TLS 1.3, which encrypts data in transit. Next, enable certificate pinning in applications; this ensures your app only trusts verified servers. Equally important, avoid public Wi-Fi without a reputable VPN, because open hotspots are prime interception grounds.
Furthermore, keep devices updated and disable outdated protocols like SSL. For organizations, layered monitoring and strict access controls form the backbone of man in the middle attack prevention.
The Anatomy of a Digital Eavesdropper: How MitM Attacks Work
To better protect yourself from these vulnerabilities, it’s essential to stay informed about recent security developments, such as those discussed in our article on the ‘Update Biszoxtall‘.
At its core, a Man-in-the-Middle (MitM) attack happens when an attacker secretly positions themselves between two parties—usually a user and a server—so they can intercept or alter communication. Think of it like passing notes in class while someone quietly reads and edits them before delivery (not exactly subtle, but surprisingly effective online).
So how does this actually happen?
First, consider Wi‑Fi eavesdropping. Attackers create an “Evil Twin,” which is a fake public Wi‑Fi hotspot that mimics a legitimate one. When users connect, their traffic flows through the attacker’s device, exposing logins and messages.
Next comes DNS and ARP spoofing. DNS (Domain Name System) translates website names into IP addresses. ARP (Address Resolution Protocol) links IP addresses to physical devices. By poisoning these systems, attackers redirect victims to malicious servers without them noticing.
Then there’s SSL stripping. Normally, HTTPS encrypts web traffic. In this tactic, attackers force a downgrade to unencrypted HTTP, exposing data in plaintext.
However, some argue HTTPS alone solves this. While encryption helps, proper man in the middle attack prevention also requires certificate validation and secure network practices.
For deeper protocol basics, see https://example.com.
Fortifying the Connection: Essential Network-Level Defenses
The VPN Imperative
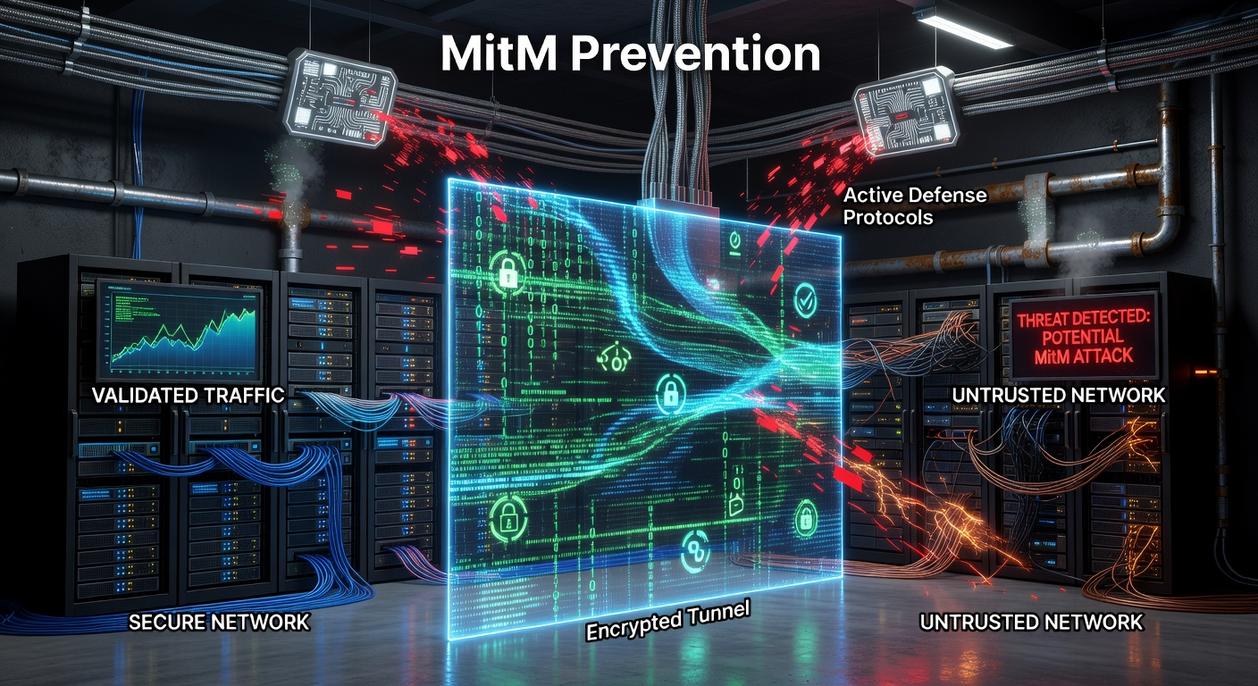
A Virtual Private Network (VPN) creates an encrypted tunnel between your device and the internet. Encryption means scrambling data so only authorized parties can read it. Without it, anyone on the same network—like a hacker at a coffee shop—can intercept traffic. This is crucial for man in the middle attack prevention, where attackers secretly relay and alter communications between two parties (the digital equivalent of someone opening and resealing your mail). ALWAYS enable your VPN before logging into banking apps, email, or cloud dashboards.
Wi-Fi Security Protocols
Not all Wi-Fi security is equal. Older protocols like WEP (Wired Equivalent Privacy) and WPA (Wi-Fi Protected Access) have known vulnerabilities and can often be cracked in minutes. WPA3, the current standard, strengthens authentication and protects against password guessing and packet sniffing.
| Protocol | Security Level | Risk Status |
|---|---|---|
| WEP | Weak |
OBSOLETE |
| WPA | Moderate | Outdated |
| WPA3 | Strong | Recommended|
If your router doesn’t support WPA3, upgrade it. (Yes, even if it “still works.”)
Public Wi-Fi Hygiene
Treat ALL public networks as hostile. Disable auto-connect features and use a VPN every time. Attackers often create fake hotspots with familiar names.
Network Segmentation
In business settings, divide networks into isolated segments. If one area is breached, attackers can’t easily move laterally. For deeper insight, read why misconfigured apis create serious security gaps.
Protocol Integrity: Implementing Strong Encryption and Authentication
I still remember the first time I inspected live traffic on a staging server and saw login credentials moving in plain text. It felt like watching someone mail their house keys on a postcard. That moment reshaped how I think about protocol integrity.
Enforcing End-to-End Encryption
First and foremost, TLS 1.3 is non-negotiable. Transport Layer Security (TLS) is a cryptographic protocol that encrypts data in transit, meaning information traveling between a client and server can’t be read or altered. TLS 1.3 improves speed and removes outdated, vulnerable cipher suites (RFC 8446). In practice, this ensures real man in the middle attack prevention by encrypting every byte of web traffic.
Some argue older TLS versions are “good enough.” However, downgrade attacks and legacy vulnerabilities say otherwise. If browsers, banks, and major cloud providers mandate TLS 1.3, that’s not paranoia—it’s pattern recognition.
HTTP Strict Transport Security (HSTS)
Next, HSTS instructs browsers to communicate only over HTTPS. In simple terms, it tells the browser, “Never knock on the insecure door again.” This blocks SSL stripping attacks, where attackers try to force a user onto HTTP. It’s a small header with outsized impact.
Certificate Pinning and Mutual Authentication
To strengthen trust further:
- Certificate Pinning hard-codes trusted certificates into an app, preventing spoofed certificate attacks.
- Mutual Authentication requires both client and server to verify identities, often using client-side certificates.
While critics say pinning complicates certificate rotation, the added assurance can be worth it in high-risk environments (think fintech or healthcare APIs). Pro tip: automate certificate lifecycle management to avoid painful outages.
Ultimately, strong encryption and authentication aren’t optional upgrades—they’re foundational safeguards.
The Human Firewall: Device Optimization and User Best Practices
When it comes to security, your biggest strength—or weakness—is you. A human firewall means trained, alert users who recognize threats before software does.
Take phishing vs. skepticism. In many MitM setups, attackers trick users into installing fake certificates or “security updates.” Click blindly, and you’ve opened the door. Pause, verify the sender, and you shut it.
Consider browser warnings: Ignore vs. Investigate. Clicking through a certificate error is like ignoring a smoke alarm (it’s rarely a false symphony). Investigating protects your data.
Outdated vs. patched systems? Unpatched software contains known vulnerabilities (CISA regularly catalogs exploited flaws). Updated devices close those gaps.
Finally, basic antivirus vs. advanced network monitoring. Tools that detect ARP spoofing strengthen man in the middle attack prevention.
Pro tip: Enable automatic updates everywhere possible.
Start by reinforcing the basics: encrypt traffic with VPN and TLS, validate endpoints through HSTS and certificate pinning, and stay alert to suspicious prompts. Together, these layers close common gaps. After all, one weak link—an open Wi‑Fi network or a dismissed browser warning—can unravel everything. With consistent man in the middle attack prevention and smart habits, you gain lasting privacy, stronger trust, and confidence your data stays confidential. That advantage compounds over time for users.
Stay Secure in an Evolving Threat Landscape
You came here looking for clarity on how to defend your systems against interception threats—and now you understand how attackers exploit weak encryption, unsecured networks, and misconfigured protocols to compromise sensitive data. More importantly, you’ve seen why man in the middle attack prevention is not optional in today’s hyper-connected environment.
Ignoring these vulnerabilities can lead to breached credentials, stolen data, and costly downtime. The longer gaps remain unpatched, the greater the exposure. Acting now protects not just devices, but trust, performance, and long-term reliability.
Start by enforcing HTTPS everywhere, implementing certificate pinning, strengthening network monitoring, and keeping all devices and dependencies updated. Then go deeper—audit your protocols, test for weaknesses, and optimize configurations before attackers find them.
If you’re ready to eliminate blind spots and harden your infrastructure, explore proven security frameworks and advanced monitoring tools trusted by industry leaders. Secure your network today—before someone else tests it for you.


 There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Kylor Vornhaven has both. They has spent years working with missed protocol vulnerabilities in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Kylor tends to approach complex subjects — Missed Protocol Vulnerabilities, Tech Evolution Echoes, Expert Insights being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Kylor knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Kylor's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in missed protocol vulnerabilities, that is probably the best possible outcome, and it's the standard Kylor holds they's own work to.
There is a specific skill involved in explaining something clearly — one that is completely separate from actually knowing the subject. Kylor Vornhaven has both. They has spent years working with missed protocol vulnerabilities in a hands-on capacity, and an equal amount of time figuring out how to translate that experience into writing that people with different backgrounds can actually absorb and use.
Kylor tends to approach complex subjects — Missed Protocol Vulnerabilities, Tech Evolution Echoes, Expert Insights being good examples — by starting with what the reader already knows, then building outward from there rather than dropping them in the deep end. It sounds like a small thing. In practice it makes a significant difference in whether someone finishes the article or abandons it halfway through. They is also good at knowing when to stop — a surprisingly underrated skill. Some writers bury useful information under so many caveats and qualifications that the point disappears. Kylor knows where the point is and gets there without too many detours.
The practical effect of all this is that people who read Kylor's work tend to come away actually capable of doing something with it. Not just vaguely informed — actually capable. For a writer working in missed protocol vulnerabilities, that is probably the best possible outcome, and it's the standard Kylor holds they's own work to.